While we strive to keep the information up to date and correct, we make no representations or warranties of any kind, express or implied, about the completeness, accuracy, reliability, suitability, or. A detailed methodology for calculating the risk posed by software vulnerabilities. Web free vulnerability management policy template. Montana currently participates in the cisa cyber hygiene services including vulnerability scanning of our external facing network assets. As both an example and a starting point, esecurity planet has developed a free vulnerability management policy template for.
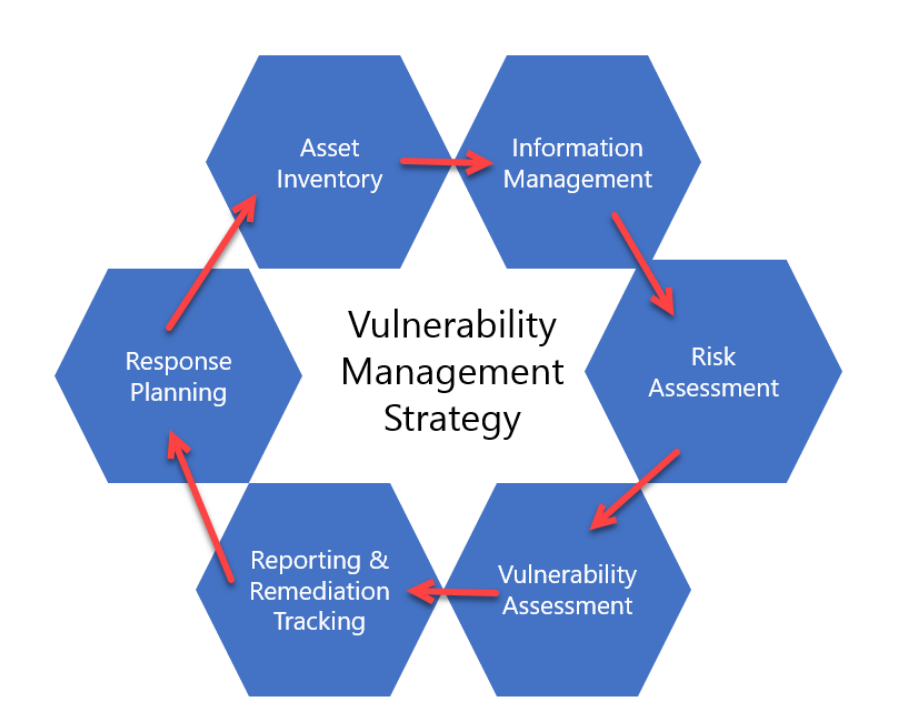
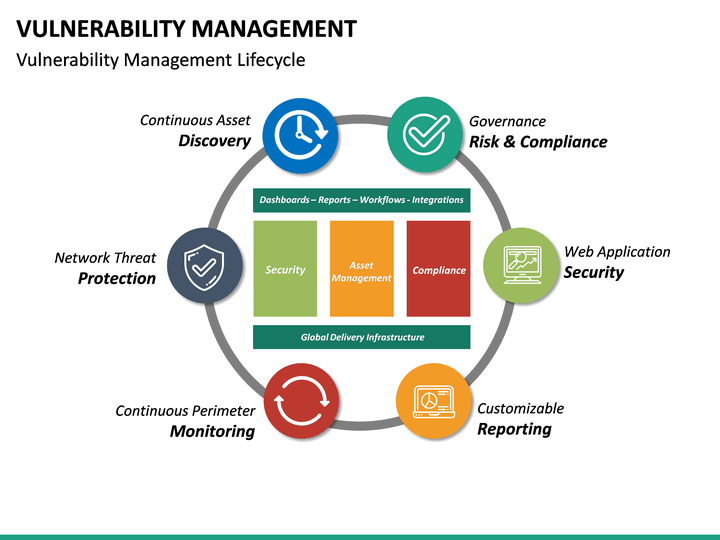
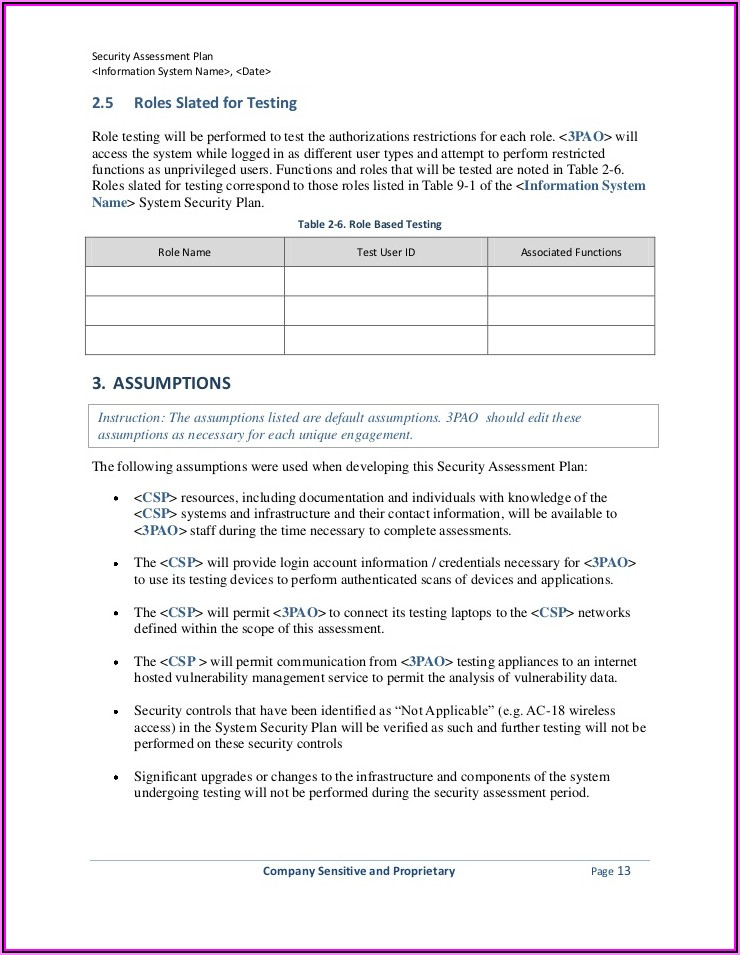
The process areas described include • developing a vulnerability analysis and resolution strategy • developing a vulnerability management plan • developing a vulnerability discovery capability To help you get started creating a policy for your organization, we’ve created a customizable template that you can download below. Determining the likelihood and magnitude of harm from unauthorized access, use, disclosure, disruption, modification, or destruction of the system, the information it processes, stores, or transmits, and any related information; You should be able to outline the next steps. A comprehensive guide for systematic detection, mitigation, and review of risks.
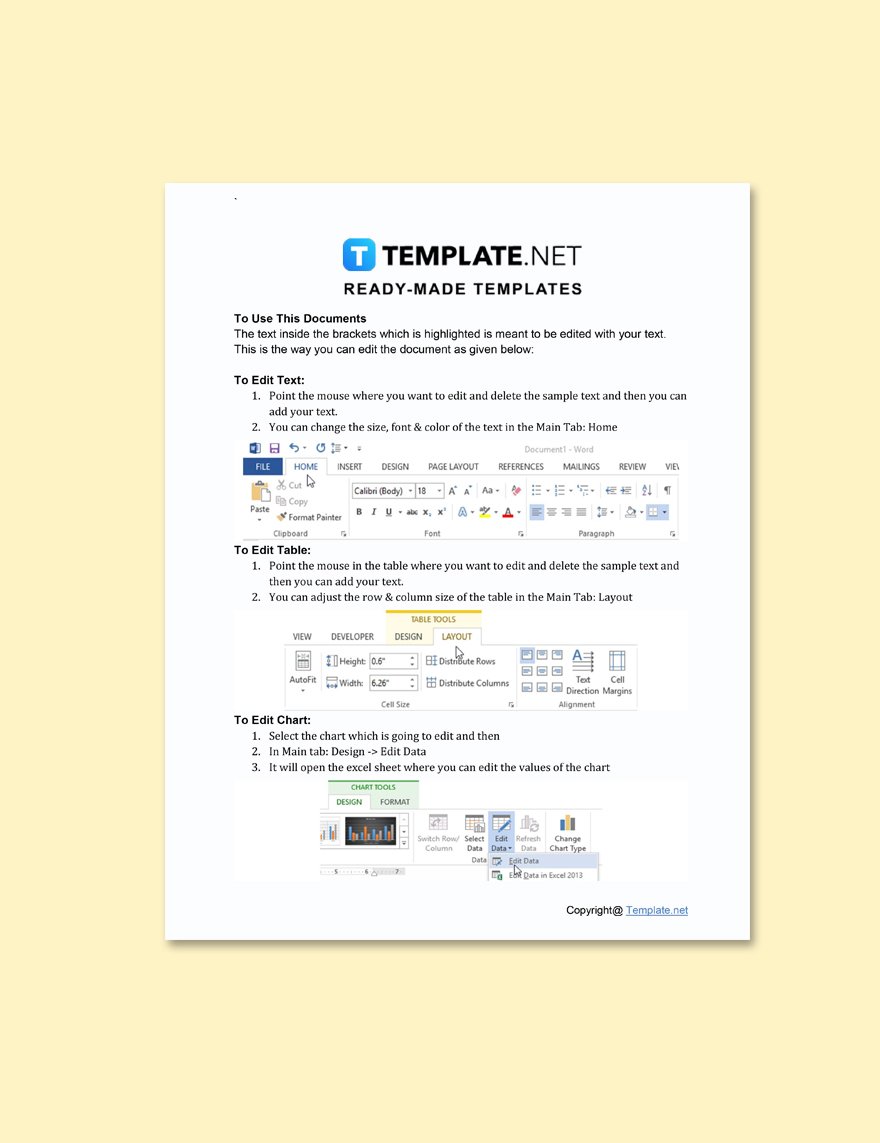
Any articles, templates, or information provided by smartsheet on the website are for reference only. A comprehensive guide for systematic detection, mitigation, and review of risks. It provides a comprehensive framework to create a detailed plan that outlines the steps and resources required to identify and address system vulnerabilities. Establish a list of assets that need protection. Web this guide is intended for organizations seeking help in establishing a vulnerability management process.
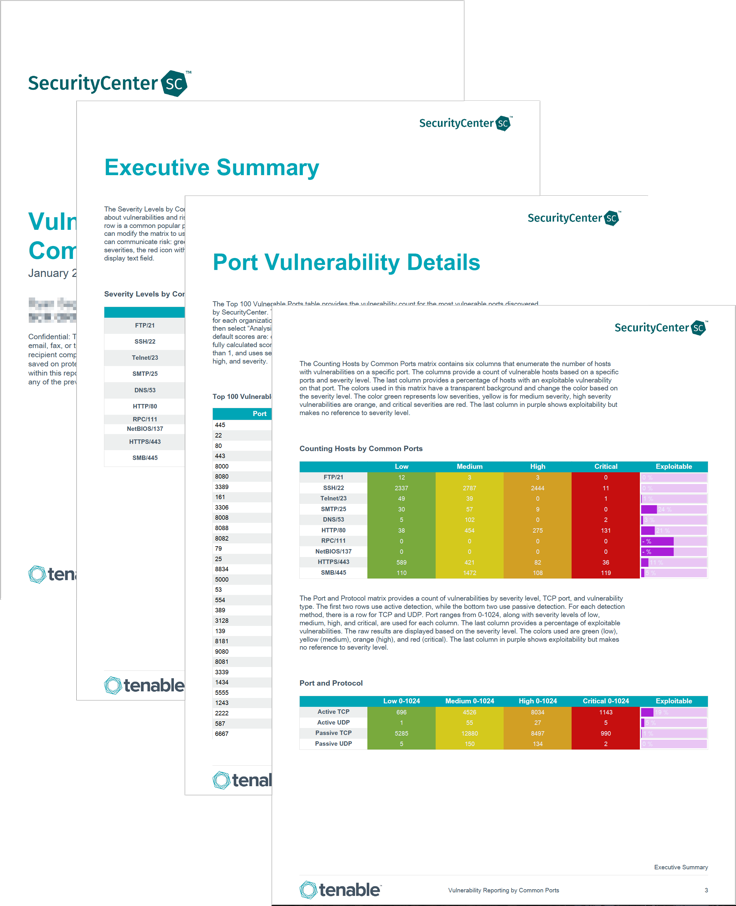
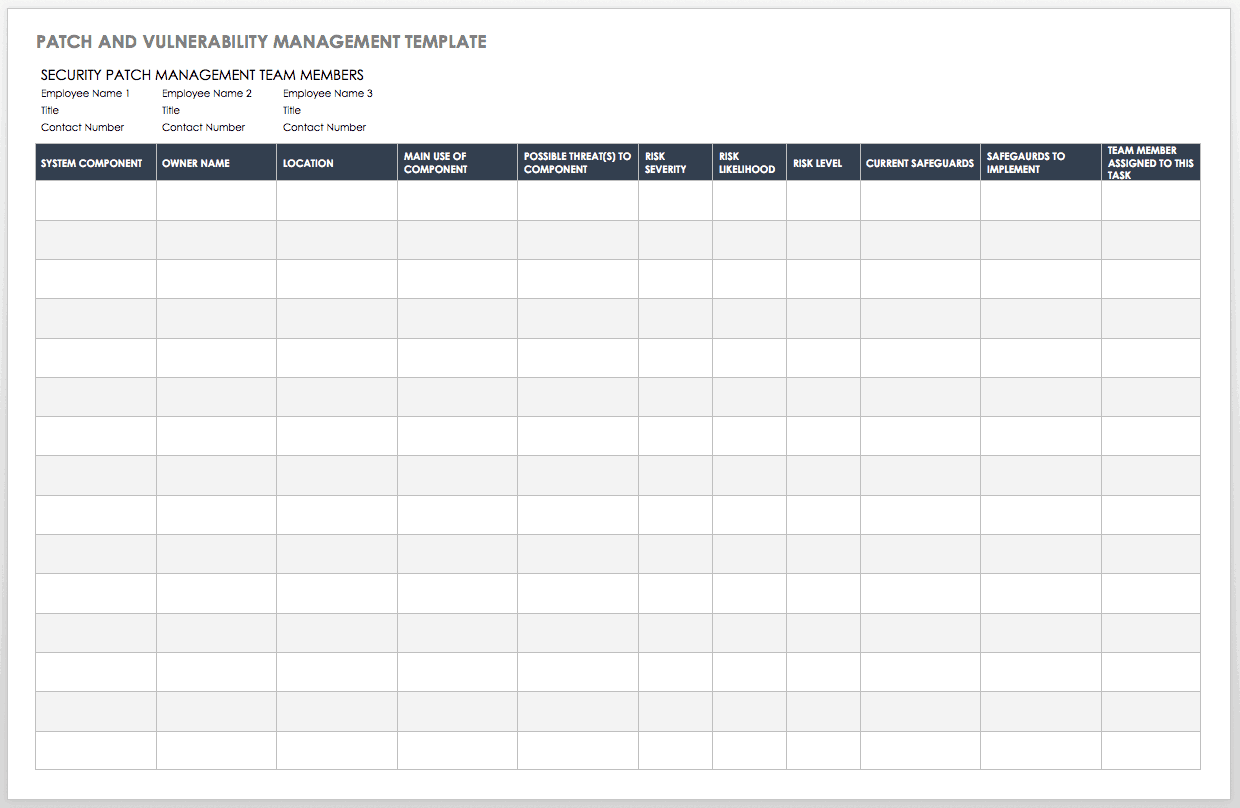
Web understanding and managing vulnerabilities is a continuous activity, requiring focus of time, attention, and resources. Web optimize your security with our vulnerability management plan template. List weaknesses to be addressed along with remediation plans, deadlines and milestones, risk levels, and status updates. The plan outlines the various vulnerability identification processes that feed into the program. Identify all systems, applications and data to be assessed. You should be able to outline the next steps. Web completing the scope task, you should be able to explain to your management and your peers why vulnerability testing is needed and how it benefits the business. Web enhance your cybersecurity with our vulnerability management template, a comprehensive guide for identifying, prioritizing, resolving, and documenting vulnerabilities. Web the sans vulnerability management maturity model helps you gauge the effectiveness of your vulnerability management program. Web the guide provides in depth coverage of the full vulnerability management lifecycle including the preparation phase, the vulnerability identification/scanning phase, the reporting phase, and remediation phase. Web security patch management team members. Web free vulnerability management policy template. It provides a comprehensive framework to create a detailed plan that outlines the steps and resources required to identify and address system vulnerabilities. The process areas described include • developing a vulnerability analysis and resolution strategy • developing a vulnerability management plan • developing a vulnerability discovery capability This policy template is meant to supplement the cis controls v8.
Web Optimize Your Security With Our Vulnerability Management Plan Template.
Web this guide is intended for organizations seeking help in establishing a vulnerability management process. Web this vulnerability management plan template provides a structure and guidance to help create a comprehensive plan that identifies and mitigates security risks, threats, and other potential issues. This policy template is meant to supplement the cis controls v8. Identify key performance indicators (kpis) for tracking the progress of the vulnerability management process.
While We Strive To Keep The Information Up To Date And Correct, We Make No Representations Or Warranties Of Any Kind, Express Or Implied, About The Completeness, Accuracy, Reliability, Suitability, Or.
Establish a list of assets that need protection. Web security patch management team members. Web create a vulnerability assessment action plan template that focuses on remediation. You should be able to outline the next steps.
Any Articles, Templates, Or Information Provided By Smartsheet On The Website Are For Reference Only.
Web free threat & vulnerability management templates for organizations to effectively identify and mitigate security risks internally. Web vulnerability management policy template. Web conduct a risk assessment, including: Web understanding and managing vulnerabilities is a continuous activity, requiring focus of time, attention, and resources.
Identify And Outline The Scope Of The Assessment.
Web evaluate the current level of security risk and create a plan for reducing or eliminating it. Identify all systems, applications and data to be assessed. Web we've created a vulnerability management policy template to help organizations assess and patch security vulnerabilities. Define the criticality of each asset.