During this process we have taken the opportunity to take a holistic look at our content and how we structure our guides. Web the user access review process (uar) refers to periodically reviewing each user’s privileges and access rights to all data and apps within an organization. Web a user access review is the review and approval of permissions granted to users within an organization's critical business applications. Web the primary purpose of user access reviews is to verify that the access privileges assigned to users align with their assigned roles and to reduce unnecessary permissions granted to employees. Check compliance with security policies.
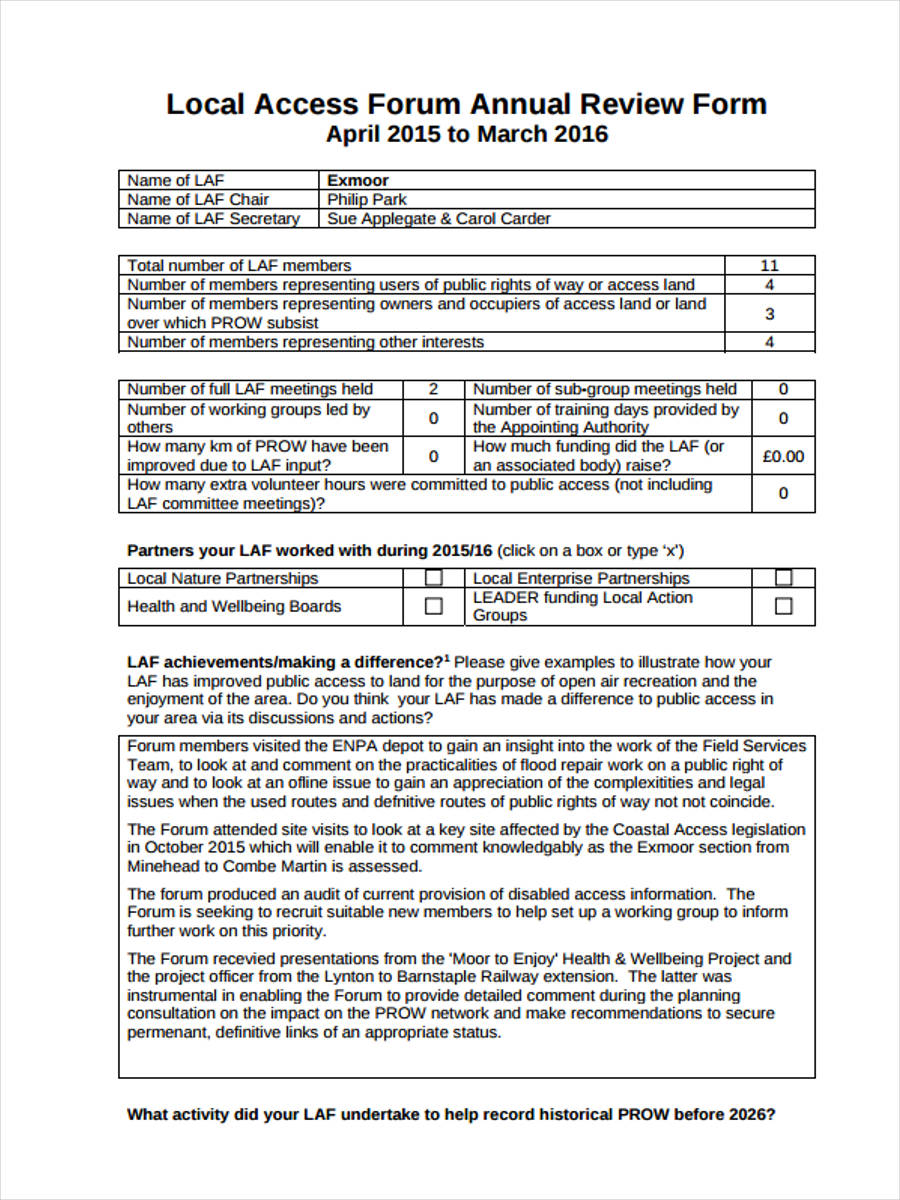
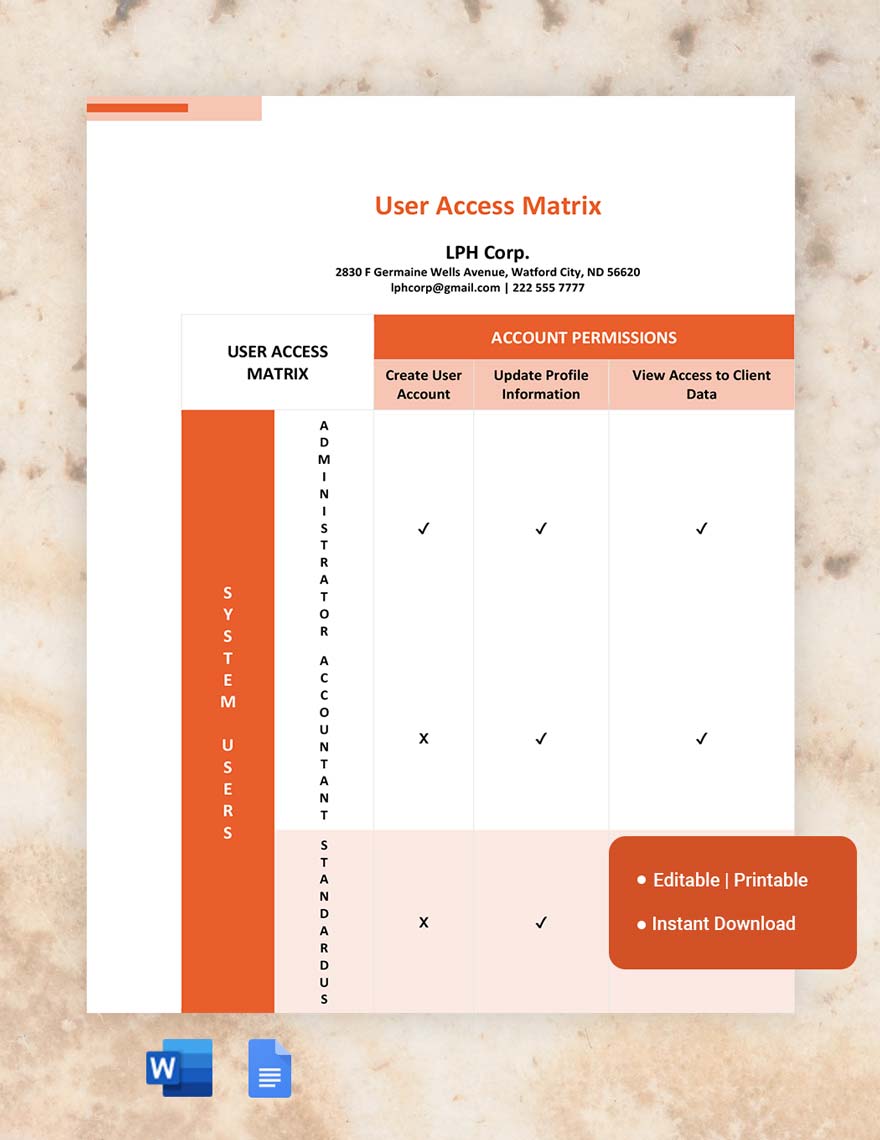
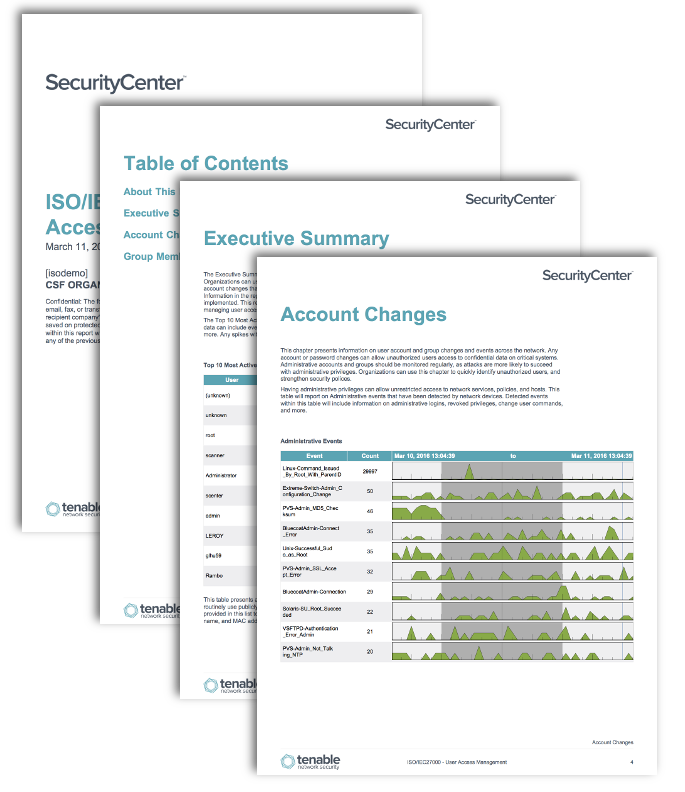
Gather information about the accounts. This review ensures that individuals have appropriate access levels to perform their job responsibilities effectively while mitigating the risk of unauthorized access to sensitive information. Web user access review is a control to periodically verify that only legitimate users have access to applications or infrastructure. Web user access review template. Web a user access review (uar) is a critical process that involves examining and validating user access rights within an organization’s systems and applications.
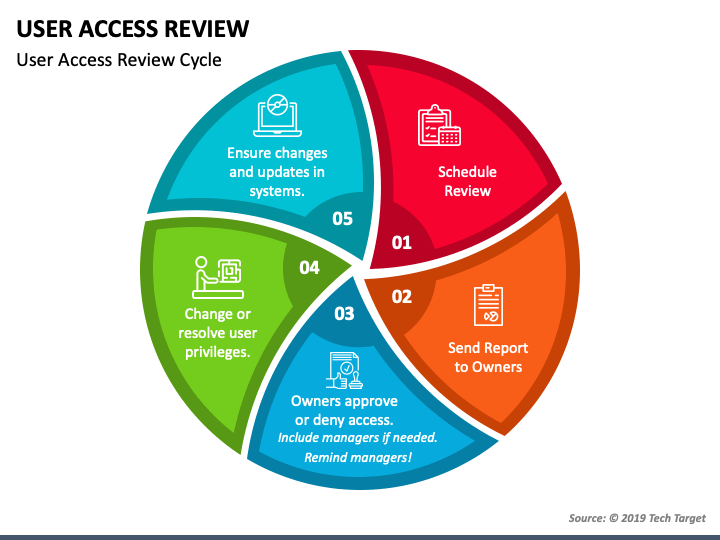
The user has access to the url for the template. Web the user access review process (uar) refers to periodically reviewing each user’s privileges and access rights to all data and apps within an organization. It helps minimize unnecessary risk, maintain tight security, and meet mandated regulatory compliance like soc, gdpr, hipaa, and nist. Web the user access review template is a document that provides a structured framework for this process. Web access reviews are regular audits of user permissions within an organization's software landscape.
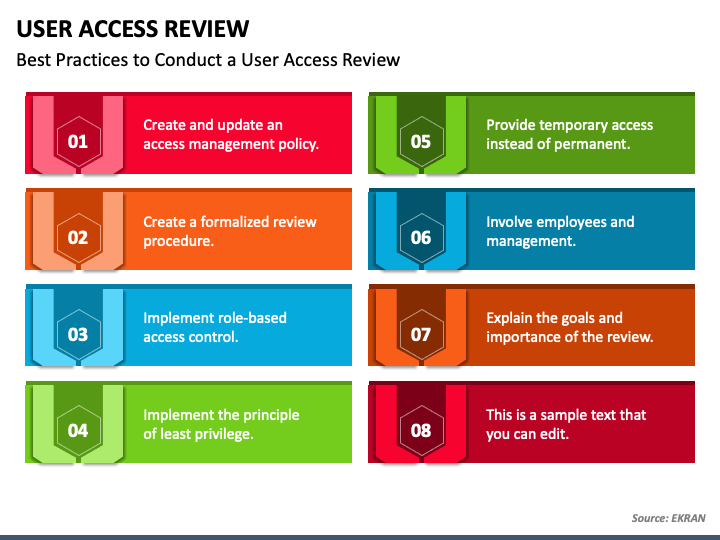
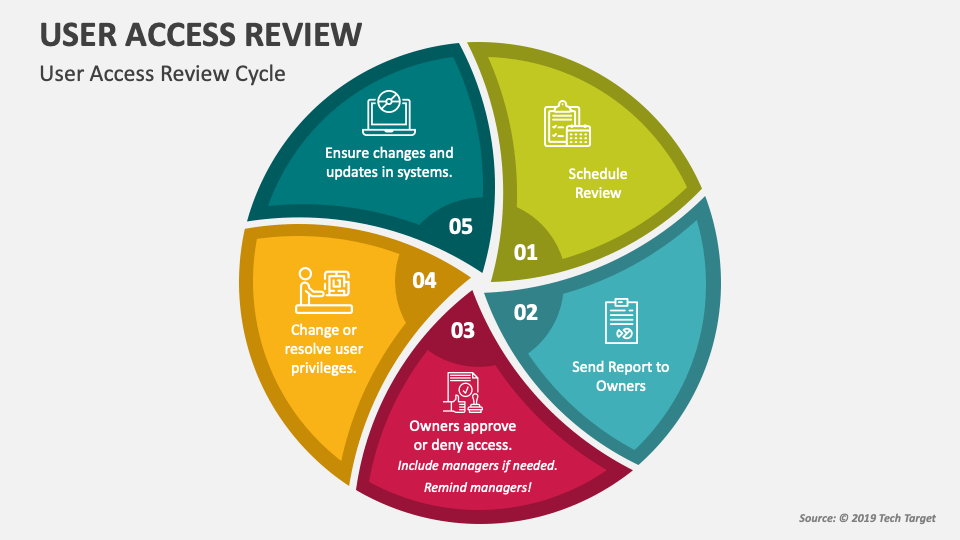
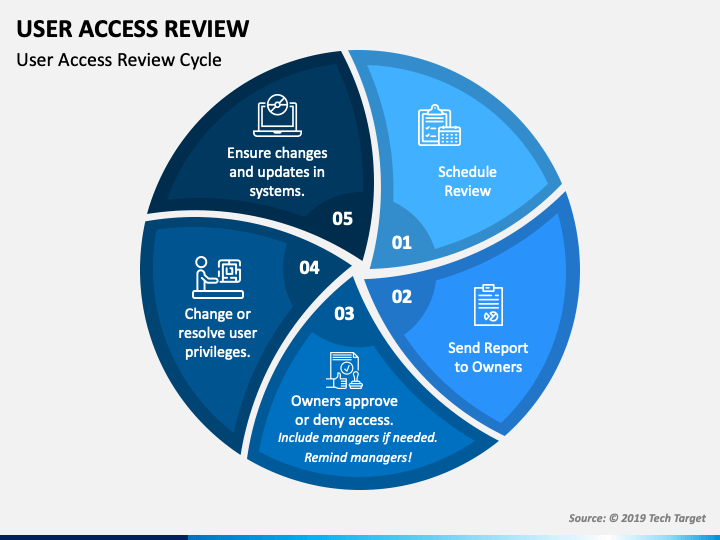
During a user access review, an application business or it owner may discover that users who left the enterprise or transferred to another team in the enterprise continue to have access to applications or. Who should be involved and what are their roles? Web a user access review template provides a structured framework for systematically assessing and validating user access rights, identifying any discrepancies or anomalies, and taking prompt corrective actions. The process of periodically reviewing the rights of anyone who has access to enterprise systems and data. We’ve gathered six best practices for advancing your organization’s user access reviews. Web a user access review policy is a crucial framework for it managers to proactively manage access privileges in response to the increasing threat of data breaches and regulatory requirements. Verification of account data integrity. Web a user access review template provides it teams with a structured format for quickly conducting reviews. What is the purpose of creating my review campaign? Ask yourself these simple but crucial questions based on your chosen strategy: A proactive approach to access reviews can be a powerful deterrent against potential internal security incidents. Gather information about the accounts. Conducting a user access review is necessary for the access management process. Web a user access review checklist is designed to guide you through the uar process systematically—guaranteeing that no critical steps are missed and that all aspects of user access and permissions are reviewed. Ready to implement user access reviews at your organization?
We’ve Gathered Six Best Practices For Advancing Your Organization’s User Access Reviews.
Ready to implement user access reviews at your organization? Web welcome to turnitin guides. Web a user access review template provides it teams with a structured format for quickly conducting reviews. Web user access review template.
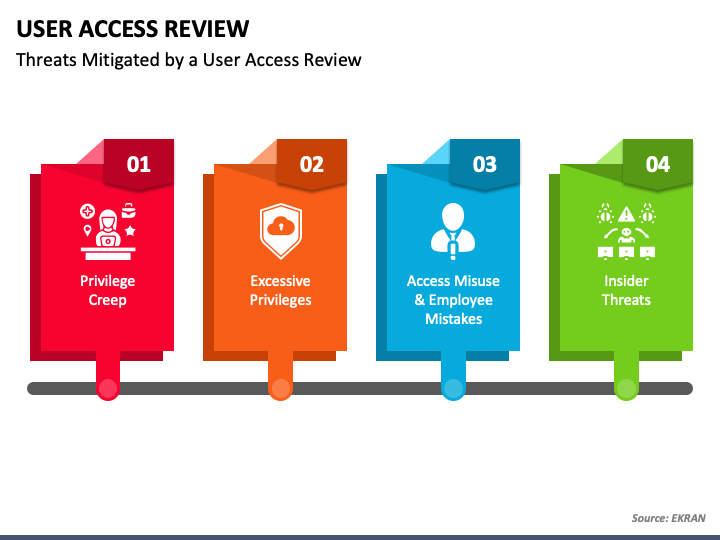
Web User Access Reviews Help Identify And Address Unauthorized Or Excessive Access, Reducing The Risk Of Insider Threats.
Welcome to turnitin’s new website for guidance! Web the user access review template is a document that provides a structured framework for this process. Web user access review template. This review ensures that individuals have appropriate access levels to perform their job responsibilities effectively while mitigating the risk of unauthorized access to sensitive information.
During This Process We Have Taken The Opportunity To Take A Holistic Look At Our Content And How We Structure Our Guides.
The next person in the workflow receives an email with the docusign document link so he/she can view it. It should be used to review user accounts on an ongoing basis, as well as when changes are made or new users are added. Users can include employees, partners, third parties, service providers and vendors. From creating an access policy and involving stakeholders to embracing the principle of least privilege, here are the essential steps you can take to complete a user access review.
It Helps Minimize Unnecessary Risk, Maintain Tight Security, And Meet Mandated Regulatory Compliance Like Soc, Gdpr, Hipaa, And Nist.
Explore how secureframe's automation and ai can help you streamline and simplify compliance. Web how to create a company password policy, with template. Web the user access review process (uar) refers to periodically reviewing each user’s privileges and access rights to all data and apps within an organization. This process ensures the right individuals have appropriate access levels based on their job roles and responsibilities.