Web sans has developed a set of information security policy templates. Web we have developed a comprehensive and customizable acceptable use policy (aup) template for it administrators. These are free to use and fully customizable to your company's it security practices. Web this detailed acceptable use policy template is designed to meet the needs of [company name] while ensuring compliance with industry standards and legal requirements. Our list includes policy templates for acceptable use policy, data breach response policy, password protection policy and more.
The iso 27001 requirement for acceptable use is covered in iso 27001:2022 annex a control 5.10 acceptable use of information and other associated asset. It defines acceptable and prohibited behaviors, aiming to protect assets, ensure security, and maintain a productive work environment. Our list includes policy templates for acceptable use policy, data breach response policy, password protection policy and more. Web the acceptable use policy ensures people understand what is expected of them when using company resources. Web this detailed acceptable use policy template is designed to meet the needs of [company name] while ensuring compliance with industry standards and legal requirements.
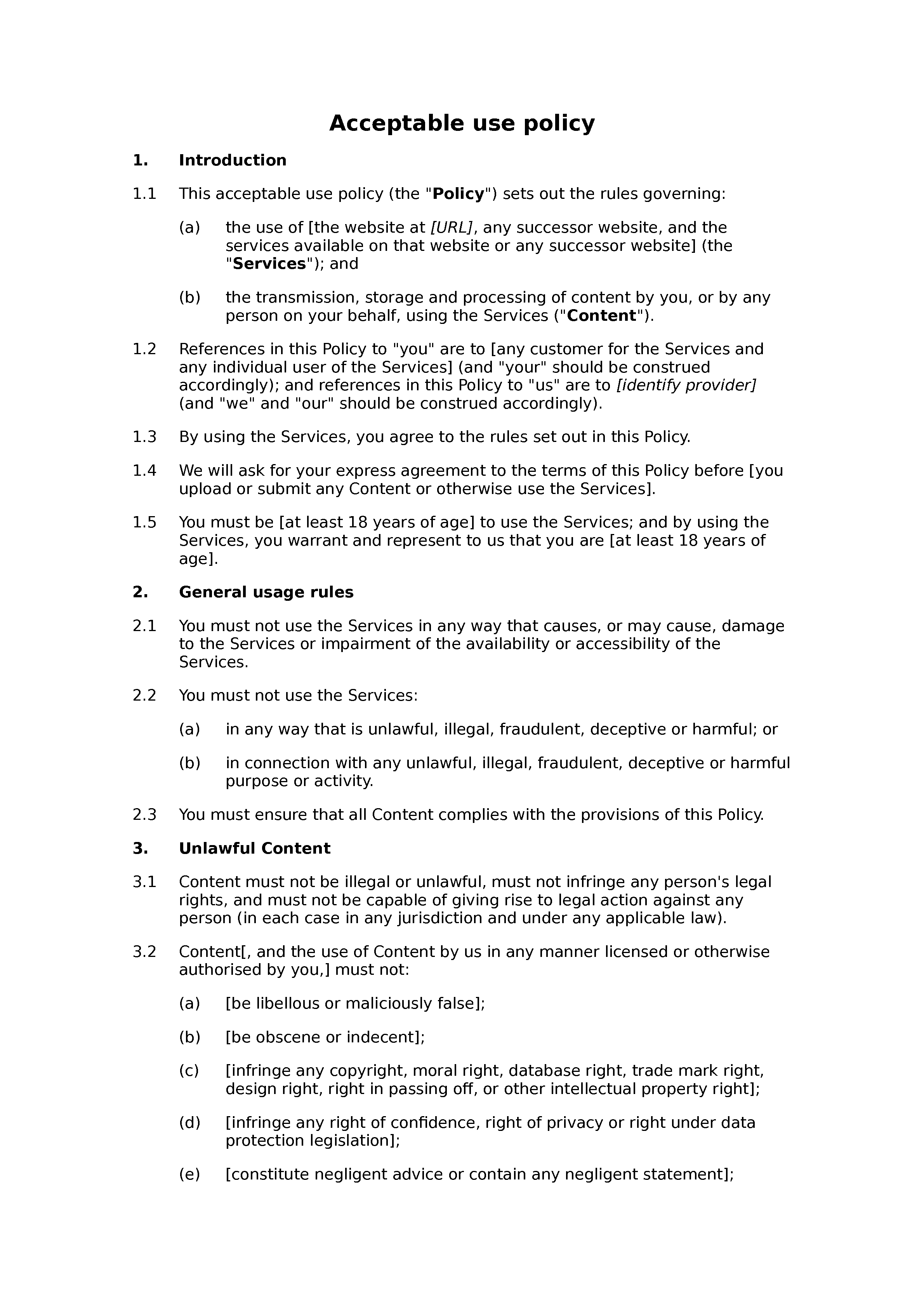
Web download our free acceptable use policy template for your website or app and learn how to fill it out properly with examples. Web sans has developed a set of information security policy templates. Web what is an acceptable use policy? By adhering to this policy, employees help maintain the security and efficiency of workplace technology resources. Our list includes policy templates for acceptable use policy, data breach response policy, password protection policy and more.
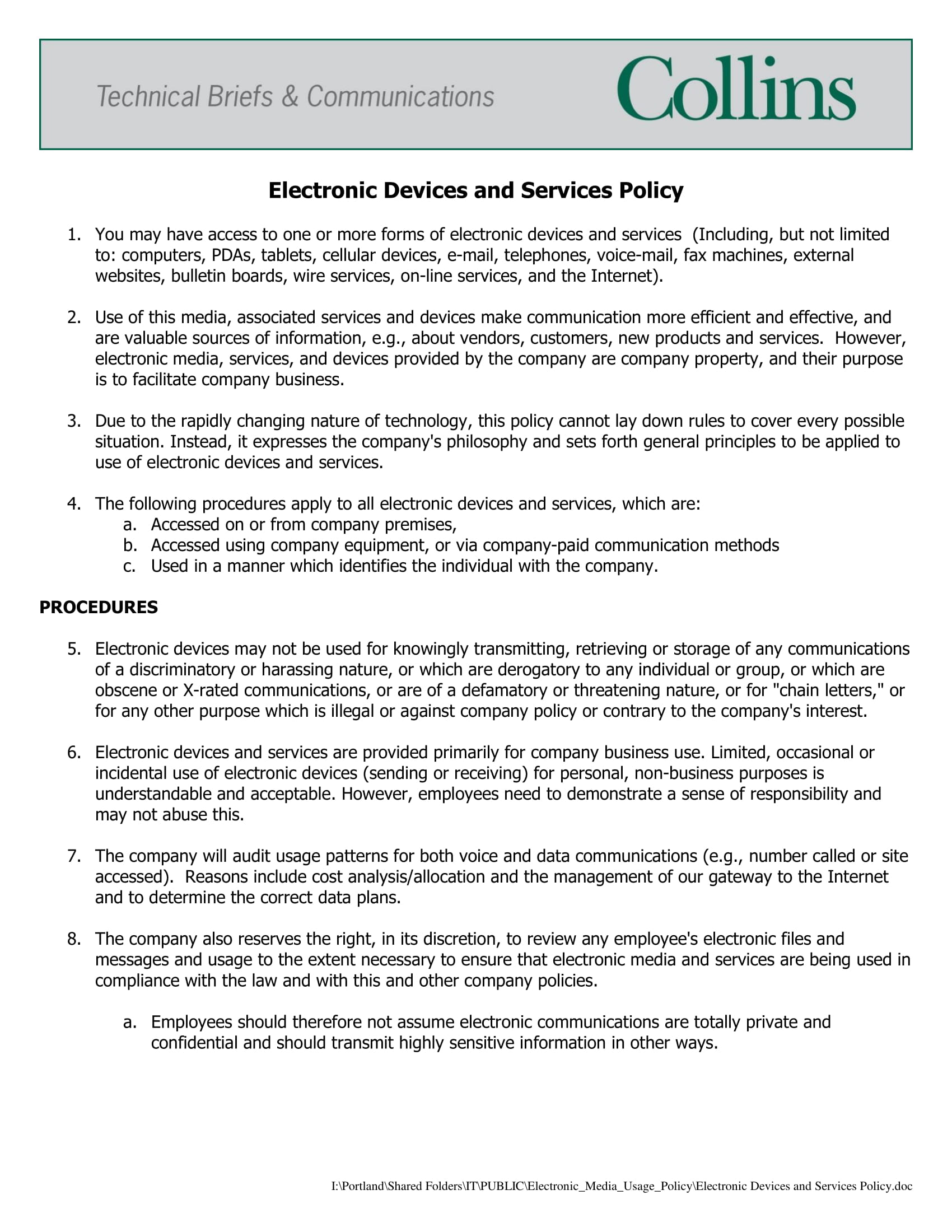
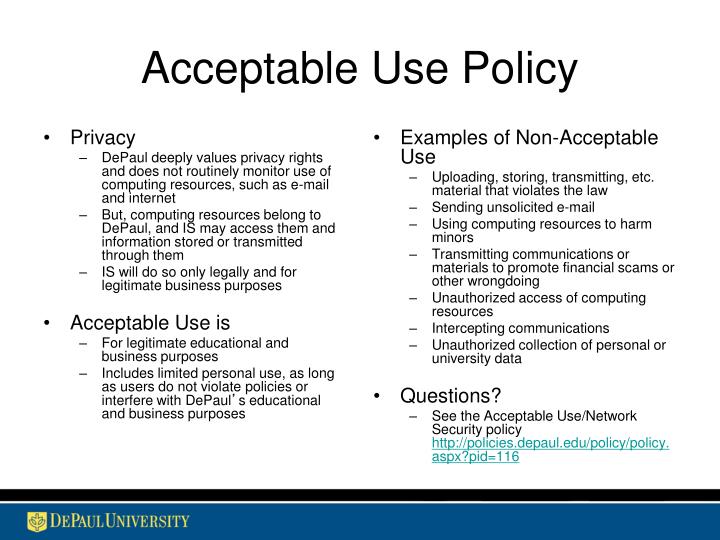
Web this acceptable use policy template is a formal company document that ensures the security of their internet environment. Web an acceptable use policy (aup) is a document outlining rules and guidelines for using an organization's it resources, including networks, devices, and software. Web the acceptable use policy ensures people understand what is expected of them when using company resources. Web what is an acceptable use policy? Web download our free acceptable use policy template for your website or app and learn how to fill it out properly with examples. The iso 27001 requirement for acceptable use is covered in iso 27001:2022 annex a control 5.10 acceptable use of information and other associated asset. Acceptable use policies outline what is appropriate and what is inappropriate when it comes to using the organization’s network and the internet. Our list includes policy templates for acceptable use policy, data breach response policy, password protection policy and more. Web this detailed acceptable use policy template is designed to meet the needs of [company name] while ensuring compliance with industry standards and legal requirements. These are free to use and fully customizable to your company's it security practices. Download our sample acceptable use policy to educate your employees about your cyber security program and protect your organization. It provides the regulations and rules for using the equipment and internet correctly and appropriately and provides sanctions if. Web we have developed a comprehensive and customizable acceptable use policy (aup) template for it administrators. Web please use these policy templates as a way to get your organization on the right track when it comes to full policy creation and adoption. It defines acceptable and prohibited behaviors, aiming to protect assets, ensure security, and maintain a productive work environment.
Web This Detailed Acceptable Use Policy Template Is Designed To Meet The Needs Of [Company Name] While Ensuring Compliance With Industry Standards And Legal Requirements.
The iso 27001 requirement for acceptable use is covered in iso 27001:2022 annex a control 5.10 acceptable use of information and other associated asset. Web sans has developed a set of information security policy templates. Web we have developed a comprehensive and customizable acceptable use policy (aup) template for it administrators. Web please use these policy templates as a way to get your organization on the right track when it comes to full policy creation and adoption.
By Adhering To This Policy, Employees Help Maintain The Security And Efficiency Of Workplace Technology Resources.
It defines acceptable and prohibited behaviors, aiming to protect assets, ensure security, and maintain a productive work environment. Web an acceptable use policy (aup) is a document outlining rules and guidelines for using an organization's it resources, including networks, devices, and software. Web download our free acceptable use policy template for your website or app and learn how to fill it out properly with examples. Our list includes policy templates for acceptable use policy, data breach response policy, password protection policy and more.
This Template Encompasses A Broad Spectrum Of Guidelines And Protocols To Ensure The Appropriate Use Of An Organization’s Network And Internet Resources.
Web this acceptable use policy template is a formal company document that ensures the security of their internet environment. Download our sample acceptable use policy to educate your employees about your cyber security program and protect your organization. These are free to use and fully customizable to your company's it security practices. Acceptable use policies outline what is appropriate and what is inappropriate when it comes to using the organization’s network and the internet.
Web What Is An Acceptable Use Policy?
Web the acceptable use policy ensures people understand what is expected of them when using company resources. It provides the regulations and rules for using the equipment and internet correctly and appropriately and provides sanctions if.



![Acceptable Use Policy Template & Examples [Free Download]](https://cdn.websitepolicies.com/wp-content/uploads/2022/03/generic-acceptable-use-policy-template.png)